Homeland Security Brief - February 2026
This brief highlights significant threats to US homeland security posed by China, Russia, Iran, and North Korea observed between January 2026 and February 2026.
Summary:
Observed Threats - Current activity that poses direct risk to US homeland security
New cyber threats observed from China, Russia, Iran, and North Korea targeting US critical infrastructure and defense industry.
A Californian political operator was sentenced for serving as an illegal Chinese foreign agent.
Three Silicon Valley engineers charged with conspiracy to sell Google trade secrets to Iran.
Horizon Threats - International activity that may pose future risk to US homeland security
A Russian cargo ship engaged in suspicious behavior near transatlantic submarine cables off the coast of the UK, amid ongoing campaign by Russian shadow fleet vessels targeting European underwater infrastructure.
Iran is reportedly developing options for attacking US interests in the event of war amid rising US-Iran tensions.
OBSERVED THREATS
Current activity that poses direct risk to US homeland security
1. CHINA, RUSSIA, IRAN, AND NORTH KOREA POSE NEW CYBER THREATS
China, Russia, Iran, and North Korea Conducting Cyber Campaigns Against the US Defense Industry
In a February 10 report, Google Threat Intelligence Group identified multiple state-sponsored hacking groups associated with Russia, China, Iran, and North Korea targeting the US defense industrial base.
Google researchers have observed social engineering campaigns by Russian actors associated with UNC5792 and UNC5976, Iranian hacking groups UNC1549 and UNC6446, Chinese actors associated with APT5, and North Korean actors associated with APT43 and UNC2970, all targeting US defense contractor employees. Common to these campaigns was the use of spoofed login pages to harvest credentials. Notable distinguishing features include UNC5792 and UNC5976's targeting of employees via Signal chat groups; UNC6446's use of resume-building tools and personality test applications to deliver malware; UNC2970's use of Google's Gemini AI to conduct reconnaissance on potential targets; and APT5's development of highly tailored phishing lures.
The report documents the following granular details found in APT5's phishing emails:
“Emails referencing a ‘Community service verification form’ from a local high school near one of the contractor’s headquarters.
“Phishing emails using ‘Alumni tickets’ for a university minor league baseball team, targeting employees who attended the university.
“Emails purporting to be ‘open letters’ to Boy Scouts of America camp or troop leadership, targeting employees known to be volunteers or parents.
“Fake guides and registration information leveraging the 2024 election cycle for the state where the employees lived.
Google also observed actors associated with Chinese hacking group UNC3236 conducting reconnaissance on the login portals of US and Canadian militaries and defense contractors.
Chinese and Iranian Hackers Embedding in US Critical Infrastructure
On February 17, operational technology cybersecurity firm Dragos announced that it had observed indications that Chinese and Iranian state-linked advanced persistent threat groups are attempting to infiltrate and proposition themselves for attacks on US critical infrastructure and critical industries. The groups include Chinese threat actors Voltzite, Sylvanite, and Azurite, as well as a suspected Iranian threat actor group Pyroxene.
All groups are believed to be engaged in efforts to map the operational processes of US companies and industries to exfiltrate data and lay the groundwork for future debilitating attacks. Voltzite and Sylvanite have been observed targeting critical civilian infrastructure such as US public utilities. Azurite has been identified targeting US companies in the manufacturing, oil and gas, pharmaceutical, and defense industries. Pyroxene has been observed targeting US maritime, aerospace and defense companies.
Additional Information:
Chinese threat actors UNC3236 and Voltzite are associated with the Volt Typhoon threat group, identified by the Five Eyes Intelligence Alliance as responsible for widespread intrusions into critical sectors of US and allied civilian critical infrastructure, primarily in communications, energy, transportation, and water systems in preparation for attacks in the event of conflict over Taiwan.1 The new reports suggest that Volt Typhoon operations continue unabated despite high-level warnings delivered by the Biden administration to China in 2024 that the group’s tactics pose an unacceptable threat to US national security, and subsequent claims by the FBI to have shut down the group’s operations.
-
China has publicly denied any association with Volt Typhoon, but has reportedly privately acknowledged that the group’s operations are meant to pressure the US to concede to Chinese interests on Taiwan.
In a follow-on report released February 12, Google researchers documented Chinese threat actors APT31, APT41, and UNC795, as well as Iranian threat actor APT42, using Gemini AI to plan and execute automated offensive cyber operations via AI agents. Notably, APT31 used Gemini in conjunction with Hexstrike penetration testing tools to automate intelligence gathering on network vulnerabilities.
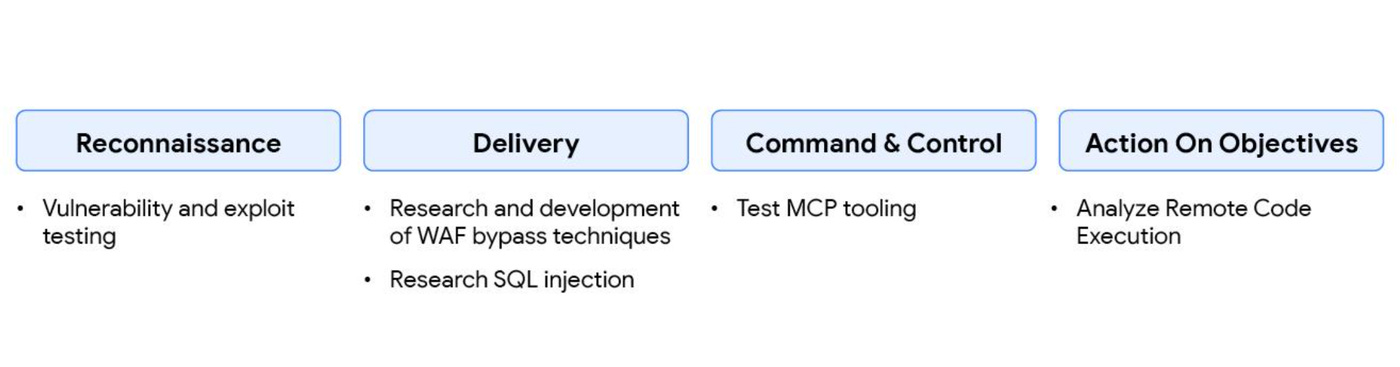
APT31 use of Gemini AI and Hexstrike to conduct automated cyber attacks. Source: “GTIG AI Threat Tracker: Distillation, Experimentation, and (Continued) Integration of AI for Adversarial Use” by Google Threat Intelligence Team, February 12, 2026
2. CALIFORNIA POLITICAL CAMPAIGNER SENTENCED FOR CARRYING OUT ORDERS OF CHINESE INTELLIGENCE
On February 9, Yaoning “Mike” Sun, was sentenced to four years in federal prison for serving as an illegal agent of the People’s Republic of China. Sun had been secretly acting on orders of the Chinese government while acting as senior political advisor to a local politician—allegedly the mayor of the city of Arcadia in Los Angeles County, California, Eileen Wang. Sun used his position to spread pro-PRC propaganda and serve Chinese national interests. According to the US Department of Justice, Sun also conducted surveillance and intimidation of local Chinese communities on behalf of PRC intelligence officers based at the Chinese Consulate in Los Angeles, targeting individuals perceived as sympathetic to Taiwan.
“Throughout 2023 and 2024, Sun communicated with an official at the consulate general of the People’s Republic of China in Los Angeles regarding activities in Southern California related to Taiwan.
“In April 2023, President Tsai Ing-Wen of Taiwan visited Southern California. Sun sent real-time updates on President Tsai’s movements to a Los Angeles-based PRC consular official and sought approval from this official to publish an article about President Tsai’s visit on the website he operated with Individual 1. Sun also took photographs of individuals protesting in support of and opposition to President Tsai and sent those photographs to the consular official.”
Follow-on report connecting Mike Sun to Arcadia Mayor Eileen Wang. Source: CBS LA
Additional Information:
Sun operated with another co-conspirator, Chen Jun (aka John Chen). Chen, a former high-level Chinese intelligence officer, was sentenced to 20 months in prison in November 2024 in a separate case. In that case, Chen, along with another unregistered Chinese foreign agent, Lin Feng, tried to bribe IRS officials to revoke the tax exempt status of the Falun Gong dissident group in the US.2
Activities of Sun’s co-conspirator Chen Jun (aka John Chen) Source: Screenshot from DOJ indictment United States of America v. Yaoning Sun aka "Mike Sun," aka "Yuening Sun," Defendant. In a July 2022 bulletin, the National Counterintelligence and Security Center warned that China has identified state, local, tribal, and territorial (SLTT) governments as levels of government especially vulnerable to United Front Work operations. According to the bulletin the PRC uses a variety of official and covert means to cultivate and leverage influence among SLTT leaders to advance PRC national interests inside the United States over the long term including:
“Collecting information, including PII. To find potential opportunities and targets for influence, the PRC may methodically collect and analyze information, including personally identifiable information (PII), on U.S. state and local leaders and those close to them.
[…]
“Targeting officials to exploit later. The PRC may target U.S. state and local leaders early in their careers and seek to use them to advocate for PRC interests should they achieve higher office.
[…]
“Exploiting partnerships. The PRC may also exploit city-to-city partnerships between the United States and China, which are managed on the Chinese side by CPAFFC. Often called “sister” relationships, they can include business, technical, cultural, and educational exchanges between U.S. and Chinese communities. Last year, a PRC diplomat said China had 50 pairs of sister provinces and 231 pairs of sister cities with the United States. While there is nothing inherently nefarious about such partnerships, which have brought benefits to many U.S. communities and are used by various nations to promote international friendship, the PRC may exploit these pacts to press its agendas.
[…]
“Creating dependencies: The PRC may also view a U.S. state or localities’ economic or other challenges as a key opportunity to create a dependency, thereby gaining influence. The PRC or its proxies may use financial rewards and punishments, such as promising or withdrawing access to Chinese markets, to cultivate and leverage business and government leaders at the U.S. state and local level.
[…]
“Shaping policy via the business community. The PRC may view the U.S. business community as an especially important vector to influence local, state, and national leaders, given that companies are key constituents of and often contributors to politicians at all levels. The PRC may use market access, investments, or economic dependency as leverage, and overtly press U.S. business leaders, particularly those with commercial interests in China, to lobby Washington for policies Beijing favors.”
3. SILICON VALLEY ENGINEERS CAUGHT SELLING SECRET GOOGLE TECH TO IRAN
On February 19, the US Department of Justice announced charges against three San Jose tech engineers, working for unspecified top companies in Silicon Valley for conspiracy to sell trade secrets to Iran. The three conspirators, Samaneh Ghandali, Mohammad Khosravi, and Soroor Ghandali, allegedly leveraged previous employment at Google to obtain proprietary information from the company on mobile processor security and cryptography. According to the indictment, the group transferred hundreds of files worth of the confidential information to third parties in Iran beginning in 2023.
Additional Information:
Iran has for years attempted to obtain advanced US technology through industrial espionage in order to thwart its international isolation and spur economic development. As a 2018 report on economic espionage in cyberspace by the US National Counterintelligence and Security Center notes:
“Iran’s economy—still driven heavily by petroleum revenue—will depend on growth in nonoil industries and we expect Iran will continue to exploit cyberspace to gain advantages in these industries. Iran will remain committed to using its cyber capabilities to attain key economic goals, primarily by continuing to steal intellectual property, in an effort to narrow the science and technology gap between Iran and Western countries.”
HORIZON THREATS
International activity that may pose future risk to US homeland security
4. RUSSIAN CARGO SHIP STALKED TRANSATLANTIC CABLES
Between January 27-28, the Sinegorsk, a Russian-flagged cargo ship, sailed up the UK's Bristol Channel and anchored for approximately half a day off the northern coast of Somerset. The vessel anchored itself in close proximity to the landing points for a cluster of transatlantic cables, including the TGN-Atlantic cables that link the US and UK, before turning around and heading back out to sea. British Royal Navy and Coast Guard vessels monitored the unusual journey amid concerns that the Russian ship intended to damage the underwater cables.
Additional Information:
Russia is widely suspected of using civilian vessels as cover to surveil and sabotage undersea cables. Russian actors have been implicated in approximately a dozen incidents of damage to telecommunications cables in the Baltic Sea since 2023. The most recent incident occurred on December 31, 2025 involving the Russian flagged cargo ship Fitburg, which according to Finnish authorities dragged its anchor across the sea bed in Finnish territorial waters for “tens of kilometers” until it cut the Elisa data cable connecting Finland and Estonia.
Disruption to the TGN-Atlantic and other transatlantic cables connecting the US and UK would cause chaos in global financial markets by disrupting the flow of data between the world’s largest banks and stock exchanges in London and New York.
5. IRAN EYEING WIDESPREAD STRIKES ON US INTERESTS IN EVENT OF WAR
The New York Times reported February 22 that US intelligence and national security officials have received a growing number of indicators suggesting an Iranian response to US strikes would involve attacks by proxy groups against US and allied targets across the Middle East and potentially in Europe.
The report comes after repeated threats by Iran to conduct widespread retaliation against the US in the event of war.
Additional Information:
While the Iranian regime has not explicitly threatened the US homeland, the dynamics of the intensifying conflict with Iran suggest it is likely to attempt strikes on US territory in the event of war.
-
Unlike in the 12-Day War, a coming war with Iran would probably be far bloodier and provoke a more unrestrained response by Iranian leaders. The Iranian regime is likely to see such a war as threatening its existence as President Trump has previously encouraged Iranian protestors to topple the government and—along with other high-level US officials—openly expressed the belief that regime change would be an ideal outcome of pressure on Iran. US special envoy Steve Witkoff is also reported to have met with exiled Iranian crown prince Reza Pahlavi at President Trump’s direction, a move the Iranian regime is likely to see as particularly threatening.
As an August 2025 article in the Combating Terrorism Center at West Point’s CTC Sentinel journal by Matthew Leavitt notes, while the capabilities of Iranian proxies have been degraded in recent years, Iran has invested heavily in options for conducting attacks on the US homeland and has attempted at least 17 such attacks over the past five years alone. These plots were organized by the Islamic Revolutionary Guards Corps (IRGC) and Hezbollah and targeted US officials such as Donald Trump, Mike Pompeo, and John Bolton, as well as outspoken dissidents such as Masih Alinejad.
One disrupted plot targeting US officials involving a Pakistani national Asif Merchant. Source: NBC News
According to a June 22, 2025 National Terrorism Advisory System bulletin, an additional avenue for Iranian retaliation against US-based targets would likely come from lone wolf assailants acting on religious rulings issued by Iranian leaders calling for retaliatory violence. The August 2022 stabbing of Salman Rushdie, inspired by an outstanding fatwa issued by Iranian authorities for the author’s 1989 book “The Satanic Verses,” is a testament to the potential for similar declarations to incite violence.

Former commander of Iran’s Islamic Revolutionary Guard Corps Hossein Salami (killed by Israel in the 12-Day War) issues a statement in January 2023 threatening French magazine Charlie Hebdo referencing attack on Salman Rushdie. Charlie Hebdo was the victim of a previous jihadist attack in 2015. Source: Iran Press News Agency
Five Eyes consists of the collective intelligence services of the US, UK, Canada, Australia, and New Zealand.
The Falun Gong is a conservative Chinese spiritualist group banned in China as a cult that is now headquartered in New York State. The Falun Gong is known for promoting traditional Chinese medicine and producing performances celebrating pre-Communist China such as Shen Yun. It is also known for producing sensationalist conservative media publications such as The Epoch Times and New Tang Dynasty (NTD) TV.



