Homeland Security Brief - April 2026
This brief highlights significant threats to US homeland security posed by China, Russia, Iran, and North Korea observed between March 2026 and April 2026.
Summary:
Observed Threats - Current activity that poses direct risk to US homeland security
A new report by the intelligence and law enforcement agencies of the US and more than a dozen allied nations warned that Russian military intelligence is exploiting vulnerabilities in home routers to harvest large volumes of user data from government and military officials.
A Chinese national was arrested for illegally photographing sensitive aircraft and facilities at multiple US Air Force Bases.
A new advisory by the FBI and CISA warned that hackers affiliated with the Iranian regime are attempting to target and disrupt computer operating systems used in US industry and critical infrastructure.
Horizon Threats - International activity that may pose future risk to US homeland security
Iranian proxies continued violent attacks targeting Jewish communities and American and Israeli interests across Europe.
OBSERVED THREATS
Current activity that poses direct risk to US homeland security
1. RUSSIAN MILITARY INTELLIGENCE EXPLOITING VULNERABLE ROUTERS TO COLLECT DATA ON GOVERNMENT OFFICIALS
On April 7, the US, Ukraine and more than a dozen allied nations announced the discovery and disruption of an elaborate plot by Russian military intelligence (GRU) to compromise small at-home routers to intercept the data of military and government officials worldwide.
According to the announcement by the FBI’s Internet Crime Complaint Center the plot, conducted by cyber actors of the GRU’s 85th Main Special Service Center (85th GTsSS) including APT28, Fancy Bear, and Forest Blizzard, have been: “collecting credentials and exploiting vulnerable routers worldwide, including compromising TP-Link routers using CVE-2023-50224.” The exploit allows the attackers to change the host configuration of a router to grant them visibility into the web traffic conducted by connected devices—including encrypted traffic when users ignore certificate error warning messages.
The scheme is part of a broader dragnet operation by the Russian intelligence services to collect mass amounts of user data worldwide and then filter it for information on specific high value targets. As the announcement states:
“The GRU has harvested passwords, authentication tokens, and sensitive information including emails and web browsing information normally protected by secure socket layer (SSL) and transport layer security (TLS) encryption. The GRU has indiscriminately compromised a wide pool of U.S. and global victims and then filtered down impacted users, especially targeting information related to military, government, and critical infrastructure.”
Additional Information:
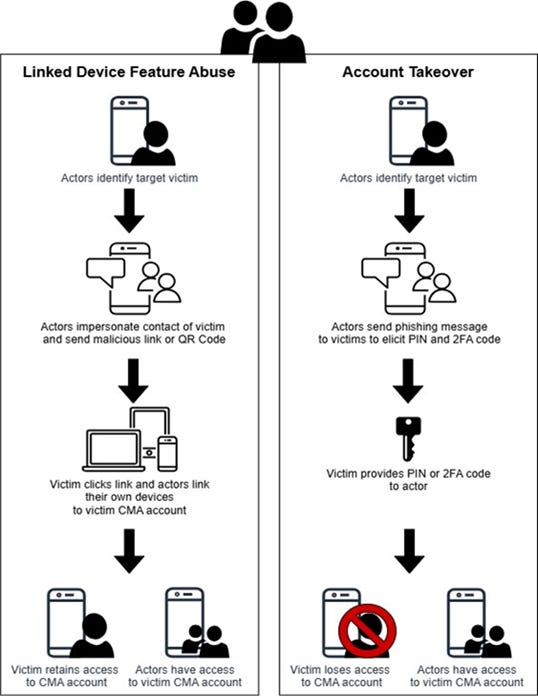
This is the second warning in two months that Russian intelligence services are exploiting cyber vulnerabilities to steal credentials from government and military officials and conduct surveillance. On March 20, 2026, the FBI and the Cybersecurity and Infrastructure Security Agency (CISA) issued a joint advisory warning that Russian hackers are conducting phishing attacks to compromise commercial encrypted messaging apps, such as Signal, used by “individuals of high intelligence value, including current and former US government officials, military personnel, political figures, and journalists.”
According to that advisory, once an account is compromised, the Russian attackers leverage the victim’s contact list to identify and target additional high-value individuals, while also collecting data to craft more convincing social engineering attacks in the future. This technically unsophisticated attack is a reminder that a user’s basic cyber security practices are just as important as end-to-end encryption for information security.
2. CHINESE NATIONAL CHARGED WITH UNLAWFUL SURVEILLANCE OF STRATEGIC US AIRBASE
On April 24, the US Department of Justice announced charges against Chinese national, Tianrui Liang, for conducting unlawful surveillance of Offutt Air Force Base in Bellevue, Nebraska. Offutt Air Force Base is a major US airbase and headquarters of US Strategic Command which commands and controls America’s nuclear arsenal. Witnesses said Liang pulled off to the side of a public road along the perimeter of the base to take pictures of planes, including the RC-135 Rivet Joint signal intelligence aircraft, E-4B “Nightwatch” National Airborne Operations Center (AKA the “Doomsday Plane”), with a camera and telescopic lens.

Liang was arrested on April 7, at John F. Kennedy International Airport in New York while attempting to leave the country for Europe. Court records indicate Liang admitted to taking photos of the base and possessed pictures of aircraft on his phone. Liang was also found to be in the possession of a small drone, which he denied using near the bases.
Liang also visited Ellsworth Air Force Base, the home of the US Air Force’s Global Strike Command, days prior to his trip to Offutt Air Force Base, with the apparent intent of viewing the base’s B-1B “Lancer” bombers.
Additional Information:
Liang, a B-1/B-2 visa holder traveling by car from British Columbia to New York may have visited other bases, and expressed an interest in also visiting Tinker Air Force Base in Oklahoma.
As noted in the Homeland Security Brief - January 2026, Chinese nationals have been implicated in dozens—and potentially hundreds—of suspicious incidents near US military bases in recent years. While some of these cases involve misunderstandings by curious tourists, the sheer number of incidents, combined with individual cases involving suspicious circumstances like Tianrui Liang suggest a pattern of coordinated crowd-sourced intelligence collection by Chinese authorities.
-
Another recent case involved a Chinese national named Qilin Wu who was charged on January 7 for illegally photographing US B-2 “Spirit” Bombers at Whiteman Air Force Base in Missouri.
3. IRANIAN HACKERS TARGETING INDUSTRIAL COMPUTERS USED FOR CRITICAL INDUSTRY AND INFRASTRUCTURE
On April 7, a new joint cybersecurity advisory issued by the Federal Bureau of Investigation (FBI) and co-signed by several federal agencies warned that since March 2026, Advanced Persistent Threat (APT) actors affiliated with the Iranian regime have been attempting to use cyber operations to disrupt US critical industries and critical infrastructure. The Iranian APTs have focused their efforts on the exploitation of software vulnerabilities at the endpoints of programmable logic controllers (PLC)—large industrial computers typically used to automate complex productive processes. PLCs are widely used in manufacturing and in several sectors of critical infrastructure including waste water and sewage, government services and facilities and energy.
Iranian groups appear to have focused their efforts most closely on systems produced by Rockwell Automation and Allen-Bradley.
According to the advisory:
“Iranian-affiliated APT actors are targeting internet-exposed PLCs with the intent to cause disruptions—including maliciously interacting with project files, and manipulating data displayed on HMI and SCADA displays—to U.S. critical infrastructure organizations. Iranian-affiliated APT targeting campaigns against U.S. organizations have recently escalated, likely in response to hostilities between Iran, and the United States and Israel.”
Additional Information:
Iranian APTs have previously targeted the PLCs in US industry and infrastructure. Attacks beginning around November 2023 by Iranian group "CyberAv3ngers” compromised at least 75 PLC and human machine interface (HMI) devices made by Israeli company Unitronics used in multiple sectors of US critical infrastructure.
Water and wastewater systems appear to be a preferred target for Iranian APTs. In addition to the present attacks, the 2023 “CyberAv3ngers” campaign caused disruptions at the Municipal Water Authority of Aliquippa in western Pennsylvania affecting over 6,000 customers. This is likely because the sector includes a large number of small operators that lack the robust IT support available to large municipalities and may be seen as easy targets.
HORIZON THREATS
International activity that may pose future risk to US homeland security
4. IRANIAN PROXY ACTIVITIES CONTINUE IN EUROPE
There have been numerous additional violent or disruptive incidents linked to groups inspired by or associated with the Iranian regime since late March when OPFOR Journal published Homeland Security Brief - The Iranian Threat in the Wake of Operation Epic Fury.
March 23 - Jewish Ambulances Torched in London
On March 23, four ambulances from Hatzola, a volunteer Jewish emergency service, were destroyed in an arson attack in London. Pro-Iranian group “Harakat Ashab al-Yamin al-Islamiyya” (HAYI) claimed credit for the attack.
March 28 - Attempted Bombing of Bank of America Headquarters in Paris
On March 28, police in Paris disrupted an attempt to detonate an improvised explosive device in front of the Bank of America headquarters. Three teenagers between 16-17 and a 21-year old man were subsequently arrested in the plot. The adult allegedly offered the three teens between 500-1000 euros to plant the explosive as well as additional opportunities for work conducting future attacks.
Police charged all four individuals for crimes including “criminal terrorist conspiracy” and “attempted destruction in connection with a terrorist enterprise.” French prosecutors have linked HAYI with the attempted bombing.
April 4 - Explosion at pro-Israel Charity in the Netherlands
On April 4, a small improvised explosive device detonated outside a pro-Israel Christian center in the Dutch city of Nijkerk. Investigation into the attack is ongoing, but the attack resembles previous attacks attributed to HAYI in the Netherlands.
April 9 - North London Synagogue Damaged by Arson
On April 9, London’s Kenton United Synagogue was targeted in an arson attack, resulting in minor smoke damage to the building’s interior. A 17-year old and 19-year old were arrested for the attack. The 17-year old has since pleaded guilty.
April 12 - Jewish Institutions in North Macedonian Capital of Skopje Attacked
On April 12, a Synagogue and German-Jewish restaurant were damaged in arson attacks in the North Macedonian capital of Skopje.
HAYI claimed credit for the attacks. The group further noted that it deliberately targets Jewish institutions unrelated to Israel due to shared religion and communal identity, “This center is not just a local place of worship, but a link in the chain of identity and mutual support between the Jewish community and the Zionist regime…Because of the crimes of the Zionist regime, no Jew anywhere will be safe.”
April 15- London Headquarters of Top Iranian Independent Media Outlet Attacked
On April 15, the London headquarters of the independent Persian-language media organization Iran International was attacked by multiple incendiary devices. The devices landed in the building’s parking lot and caused a small fire but did not result in significant damage. Three individuals, a boy aged 16 and two men aged 19 and 21 were arrested in connection and charged with arson.
April 16 - Drone Incident Near Israeli Embassy in London
On April 16, social media accounts associated with HAYI posted a video claiming to show a drone attack on the property of the Israeli embassy in London involving dangerous chemicals. The Israeli Embassy and London Metropolitan Police denied that such an attack occurred on the embassy grounds but noted that a security incident did take place at a nearby park.
April 18 - Attempted Arson at Jewish Charity in London
On April 18, a London building previously occupied by a Jewish charity called Jewish Futures was lightly damaged in an attempted arson attack. HAYI claimed credit for the attack.
April 28 - Attempted Arson at London Memorial to Iranian Protesters
On April 28, London Metropolitan Police’s Counter Terrorism Policing unit announced it was investigating an attempted arson at a memorial wall to Iranian protesters slain by the Iranian regime. Authorities said that the incident was not yet being treated as an act of terrorism but the rash of suspicious or violent incidents targeting the Jewish community in the Golders Green neighborhood where the memorial is located were prompting investigators to keep an open mind.
April 29 - Two Jewish Men Stabbed Outside London Synagogue;
On April 29, two Jewish men in London were stabbed by a 45-year-old man in what British authorities have deemed an act of terrorism. HAYI claimed credit for the attack.
Additional Information:
While the group Harakat Ashab al-Yamin al-Islamiyya (The Islamic Movement of the Companions of the Right) has claimed credit for many of the attacks, the actual existence of the group as an independent entity has increasingly been called into question. The group notably did not exist prior to the start of the US-Israeli war on Iran. Its ability to effectively coordinate seemingly disparate activities across Europe so quickly suggests the group is actually an operation conducted by the Islamic Revolutionary Guard Corps Quds Force. Further suggestive of the link is that the arson incidents bear hallmarks of similar incendiary attacks the IRGC coordinated against Jewish targets in Australia in 2024. Those attacks resulted in Australia expelling the Iranian ambassador in August 2025 and later labeling the IRGC a state sponsor of terrorism in November.
Nicolas Stockhammer, Senior Research Fellow at The Soufan Center, notes that the Islamic Revolutionary Guard Corps Quds Force often coordinates its activities to appear to be isolated acts of antisemitic hatred, or violent extremism:
“Pro-Iranian networks drawing from ideological supporters among diaspora, radicalized teenagers, and even petty criminals form an inconspicuous facilitation web across Europe. At the epicenter of these structures, Iran’s IRGC-Quds Force pulls strings through sub-conventional proxies, enabling deniable hits on soft targets like synagogues or tourist spots, sparing Tehran direct blame and possible retaliation.”
The IRGC pays these actors small bounties for the attacks, in what has been called a form of “gig economy” terrorism.
The IRGC has attempted to coordinate similar terrorist operations in North America with less success. It has, however, made multiple attempts in recent years to recruit members of organized crime to conduct assassinations of US and foreign government officials and Iranian dissidents within the US homeland as well as in Mexico and Canada. The pattern of attempted high profile violent attacks during peacetime suggests Iran is willing to carry out terror attacks now but not yet able to do so. Seemingly confirming this intent, the spokesperson for Iran’s Armed Forces General Abolfazl Shekarchi warned on March 20 that Iran would make "parks, recreational areas and tourist destinations" unsafe for its enemies.
-
The attempt by Mehdi Taj, the head of Iran’s football federation and former commander in the IRGC, to enter Canada illustrates potential security threats Iran may pose to the upcoming World Cup. Iran may use the events to insert operatives into North America, conduct recruitment of proxies, or in a worst-case scenario, carry out attacks of terrorism.



